top of page
Our Insights
Xyfon Insights brings clarity to an increasingly complex security landscape.
We share practical perspectives from real-world assessments, testing, and advisory work.
No noise. Just insights you can act on.



Penetration Testing in 2026: Where real attacks are coming from and what most tests still miss
A penetration test in 2026 should do more than look for the usual web flaws and dump out a list of findings. Attackers are moving faster, targeting different parts of the environment, and increasingly chaining together identity, cloud, SaaS, API, and edge-device weaknesses. Google’s M-Trends 2026 says exploits remained the most common initial infection vector at 32% of intrusions, voice phishing rose to 11%, and the mean time to exploit vulnerabilities dropped to an estimated
Mar 303 min read


The Moment Most Companies Realize They Need a vCISO
Nobody wakes up and says, “we should hire a Virtual CISO.” It usually starts with something smaller. An audit gets uncomfortable. A client asks about your cybersecurity policy and nobody has a clear answer. Your IT guy says, “we’re covered,” but you’re not entirely convinced. Or worse—you get that email: “ we completed a fraudulent wire transfer. ” That’s typically the moment businesses realize they don’t have a real cybersecurity strategy. They just have tools. The issue is
Mar 223 min read

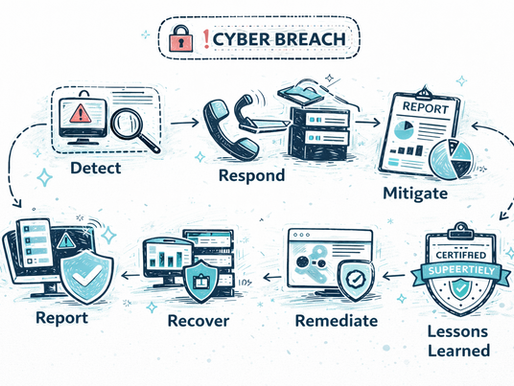
What Happens in the First 24 Hours After a Cyber Breach
No organization plans for a cyber breach—but many eventually face one. For small and mid-sized businesses, the real danger isn’t always the initial intrusion. It’s the confusion that follows. Systems may start behaving unpredictably, employees begin reporting strange activity, leadership demands answers, and the clock starts ticking. The first 24 hours after detecting a breach can determine whether the situation becomes a manageable security event or a major operational crisi
Mar 73 min read


Dormant Accounts and Permission Creep. The Hidden Cyber Risk.
Most breaches don’t start with sophisticated zero-day exploits. They start with something far more ordinary: an account that should have been disabled… but wasn’t. As businesses grow, employees change roles, contractors come and go, vendors rotate, and software tools pile up. Access is granted quickly to keep things moving. But it’s rarely reviewed with the same urgency. Over time, permissions accumulate. Accounts linger. Admin rights stick around long after they’re needed. T
Feb 232 min read


Top 10 Cloud Misconfigurations SMBs Should Be Aware Of
The cloud promised flexibility, lower costs, and faster deployments. For small and mid-sized businesses, that promise is real—but so is the risk. Misconfigured cloud environments remain one of the leading causes of breaches for SMBs. A simple misstep—a storage bucket left public, a forgotten admin API key, or weak access controls—can expose sensitive data to anyone on the internet. With hybrid and multi-cloud setups becoming the norm, even small mistakes can have outsized con
Feb 22 min read


AI-Powered Phishing in 2026: What Small businesses should be aware of
Attackers are now using AI to craft emails, texts, and even voice messages that are personalized, well-written, and context-aware. These attacks don’t spray thousands of generic messages anymore; they study your business, your vendors, your executives, and your workflows. For SMBs, this shift is especially dangerous because the attacks look legitimate and bypass traditional email filters and human intuition alike. What Makes AI-Driven Phishing Different Perfect language and
Jan 262 min read


Supply-Chain & Third-Party Cyber Risks: The Silent Threat Facing SMBs in 2026
For many small and mid-sized businesses, cybersecurity efforts focus inward—firewalls, antivirus, employee training. But in 2026, some of the most damaging breaches don’t start inside your organization at all. They start with vendors, partners, MSPs, SaaS tools, or contractors that already have trusted access to your systems. Attackers increasingly target these third parties because they know SMBs often lack visibility and control beyond their own perimeter. One compromised s
Jan 192 min read


OWASP Top 10 for LLM Applications 2025: What It Really Means for Teams Deploying Ai features
As organizations embed AI copilots, assistants, and automation into nearly every workflow, something important is becoming clear: LLMs introduce completely new security risks that traditional AppSec was never designed to handle. The newly released OWASP Top 10 for LLM Applications 2025 is the strongest signal yet that AI security is entering its own era—one where text, prompts, tools, plugins, embeddings, and datasets merge into an attack surface unlike anything before. But
Dec 10, 20252 min read
bottom of page
